React2Shell (CVE-2025-55182) Exploitation on AWS EC2 - A Real-World Incident Report
Just discovered CVE-2025-55182 exploitation on our production Next.js server.
Hi! 👋 I'm a Senior Software Engineer!
I've had the incredible opportunity to build amazing things. I've helped companies boost performance - we're talking 40% faster database queries, 30% reduced assessment processing times, and creating systems with 99.999% uptime.
But tech isn't just my job - it's my passion. When I'm not coding, you'll find me exploring blockchain technologies, contributing to open-source projects, or diving into video games. I've even developed my own projects like a blockchain explorer and an educational NFT minting platform.
I'm a big fan of writing, creating videos, and teaching. Whether it's mentoring junior developers or exploring new tech frontiers, I'm all about growth and innovation.
Executive Summary
On one of our AWS EC2 servers running a Next.js development environment, we discovered an active exploitation of the React2Shell vulnerability (CVE-2025-55182 / CVE-2025-66478). The attacker successfully installed cryptocurrency mining software with persistent cron jobs. This incident report details our discovery, response, and recommendations for the broader community.
Incident Timeline & Discovery
While investigating unusual server performance, we identified unauthorized mining activity connected to a Monero mining pool. Analysis revealed:
Mining Pool: MoneroOcean (moneroocean.stream)
Attacker's Wallet Address:
42ZUiZsAoLeLjcaYK6rYQw1jyhadoB5kk5jXY5FJKoCkWzm964rqqBuGugSjqQZDB2B3JgE1YTGcHLEVN4nHNspH1UZX4nRScope: 33+ active workers initially detected across multiple cloud providers (AWS, Azure, GCP)
Current Status: Worker count has grown to 43+ as of this writing
This indicates a widespread, ongoing campaign targeting vulnerable servers across multiple cloud platforms.
Technical Background: The React2Shell Vulnerability
What is React2Shell?
React2Shell (CVE-2025-55182) is a critical remote code execution (RCE) vulnerability with a CVSS score of 10.0 - the maximum severity rating. It affects:
React Server Components (RSC) in React 19.x
Next.js 15.x and 16.x using App Router
Next.js 14.3.0-canary.77 and later canary releases
How Does It Work?
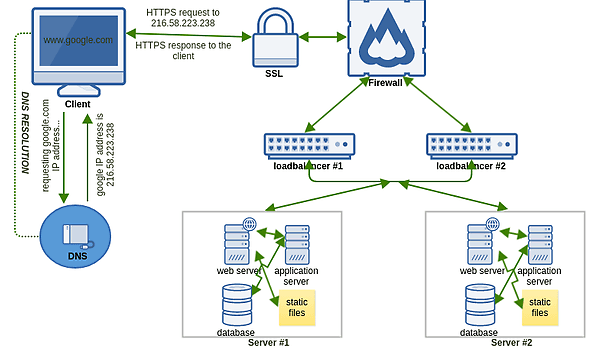
The vulnerability stems from unsafe deserialization in the React Server Components "Flight" protocol. An attacker can:
Send a single crafted HTTP POST request to any exposed Next.js App Router endpoint
Exploit the protocol's insecure handling of RSC payloads
Execute arbitrary code on the server with near-100% reliability
Establish persistence through cron jobs and backdoors
Critical Note: Default configurations are vulnerable - no code changes by developers are required for exploitation. A standard Next.js app created with create-next-app and built for production can be exploited immediately.
Attack Vector & Exploitation
What We Observed
The attacker leveraged CVE-2025-55182 to:
Initial Access: Exploited the vulnerable Next.js application endpoint
Payload Delivery: Deployed cryptocurrency mining binaries
Persistence: Created cron jobs to ensure the mining process always runs
Evasion: Implemented mechanisms to restart the process if terminated
Likely Backdoor: Given the sophistication, backdoors and additional access methods were likely established
Attempted Remediation Failures
Our initial remediation attempts were unsuccessful:
# Attempted process termination - FAILED
kill -9 <mining_process_pid>
# Process automatically restarted
# Attempted cron job removal - FAILED
crontab -e # Removed malicious entries
# Miner continued running through alternative persistence mechanisms
# Attempted package updates - FAILED
npm install next@latest
# Downloads blocked/intercepted by attacker's modifications
The attacker's persistence mechanisms and potential system-level access prevented clean remediation.
Our Response & Recovery
Decision: Complete Server Replacement
Given the severity and persistence of the compromise, we implemented a full server replacement strategy:
Provisioned New EC2 Instance: Launched a fresh instance with updated configurations
Code Migration: Deployed application code to the new instance with patched dependencies
Security Hardening: Implemented additional security controls before going live
Old Instance Termination: Completely destroyed the compromised server
Why Full Replacement?
Unknown Compromise Depth: No way to guarantee removal of all backdoors
Potential Credential Theft: SSH keys, environment variables, and secrets may have been exfiltrated
Secondary Persistence: Attacker may have established multiple persistence mechanisms
Cost-Benefit: Rebuilding was faster and more secure than forensic cleanup
Critical Consideration: Our server only hosted frontend applications with no databases or sensitive state. Had this contained databases, user data, or cryptographic keys, the impact would have been catastrophic.
Recommended Actions - Immediate
1. Check for Vulnerable Versions
Run the official scanner:
npx fix-react2shell-next
This will:
Scan all
package.jsonfiles (supports monorepos)Identify vulnerable versions of React and Next.js
Recommend specific patched versions
Optionally apply fixes automatically
2. Verify Your Versions
Vulnerable Versions:
| Framework | Vulnerable Versions | Patched Version |
| Next.js | 15.0.0 - 15.0.4 | 15.0.5 |
| Next.js | 15.1.0 - 15.1.8 | 15.1.9 |
| Next.js | 15.2.0 - 15.2.5 | 15.2.6 |
| Next.js | 15.3.0 - 15.3.5 | 15.3.6 |
| Next.js | 15.4.0 - 15.4.7 | 15.4.8 |
| Next.js | 15.5.0 - 15.5.6 | 15.5.7 |
| Next.js | 16.0.0 - 16.0.6 | 16.0.7 |
| React | 19.0 - 19.2 | 19.0.1, 19.1.2, 19.2.1 |
3. Patch Immediately
No workarounds exist - upgrading is the only solution:
# For Next.js
npm install next@<patched-version>
# For React (if using RSC directly)
npm install react@19.0.1 react-dom@19.0.1
4. Post-Patch Actions
After patching:
Rotate all secrets: API keys, database passwords, JWT secrets, etc.
Review environment variables: Assume all credentials were compromised
Audit SSH keys: Remove and regenerate all SSH access keys
Check for persistence: Look for suspicious cron jobs, systemd services, startup scripts
Monitor processes: Watch for unusual CPU usage or network activity
Review access logs: Look for suspicious HTTP POST requests to RSC endpoints
5. Deploy Runtime Detection
If using Falco or similar tools, deploy detection rules for React2Shell exploitation attempts.
Signs of Compromise
Check your servers for these indicators:
Process-Level Indicators
# Unusual CPU usage
top
htop
# Suspicious processes
ps aux | grep -E "(xmrig|monero|miner|cpuminer)"
# Network connections to mining pools
netstat -tulpn | grep -E "(moneroocean|pool\.|stratum)"
Persistence Mechanisms
# Check cron jobs
crontab -l
cat /etc/crontab
ls -la /etc/cron.*
# Check systemd services
systemctl list-units --type=service --state=running
# Check startup scripts
cat /etc/rc.local
ls -la /etc/init.d/
File System Artifacts
# Look for recently modified files
find / -mtime -7 -type f 2>/dev/null
# Check for hidden files in common directories
ls -la /tmp
ls -la /var/tmp
ls -la ~/.config
Industry Impact & Statistics
Based on security research:
39% of cloud environments contain Next.js or React in vulnerable versions
61% of environments with Next.js have publicly accessible instances
44% of all cloud environments have publicly exposed Next.js (regardless of version)
Exploitation observed across AWS, Azure, GCP, and other cloud platforms
Public RCE exploits available with near-100% reliability
References & Additional Resources
Official Advisories
Security Research
Tools
Key Takeaways
Patch immediately - This is a maximum severity (10.0) RCE with active exploitation
Assume compromise - If you're running vulnerable versions publicly, assume you've been targeted
Full rotation - Rotate all secrets, keys, and credentials after patching
Consider full rebuild - For critical systems, rebuilding may be safer than remediation
Monitor actively - Watch for signs of cryptocurrency mining or unusual activity
Stay informed - Follow security advisories for additional related vulnerabilities
Conclusion
The React2Shell vulnerability represents a critical threat to the React and Next.js ecosystem. The ease of exploitation, combined with the widespread adoption of these frameworks, has created an attractive target for threat actors.
Our incident demonstrates that attackers are actively exploiting this vulnerability at scale, targeting cloud infrastructure across multiple providers. The sophistication of the persistence mechanisms we encountered suggests organized threat actors, not just opportunistic attacks.
Do not delay patching. Every hour your vulnerable Next.js application remains exposed is an opportunity for compromise. The attacker we encountered has already compromised 40+ servers - don't let yours be next.
Have you encountered React2Shell exploitation? Share your experience in the comments or reach out to contribute to community awareness.
Update your servers. Rotate your secrets. Stay vigilant.